VPC Design Patterns
VPC design is the foundation of every AWS architecture. Get this wrong, and everything else fails:
VPC CIDR Planning (Interview Must-Know)
| CIDR Block | Total IPs | Usable IPs | Best For |
|---|---|---|---|
| /16 | 65,536 | 65,531 | Large production VPC (recommended default) |
| /20 | 4,096 | 4,091 | Medium workload, dev/staging |
| /24 | 256 | 251 | Small subnet, single-purpose |
| /28 | 16 | 11 | Smallest subnet allowed (AWS reserves 5 IPs per subnet) |
AWS reserves 5 IPs per subnet: network address, VPC router (.1), DNS (.2), future use (.3), broadcast.
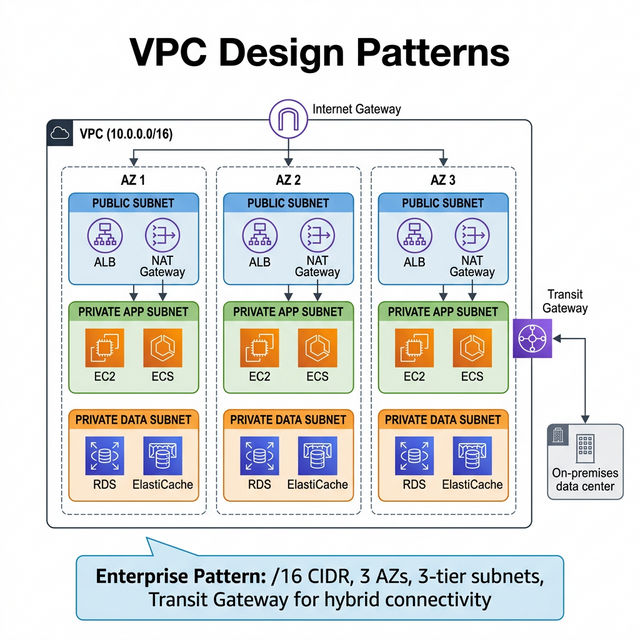
Enterprise VPC Architecture
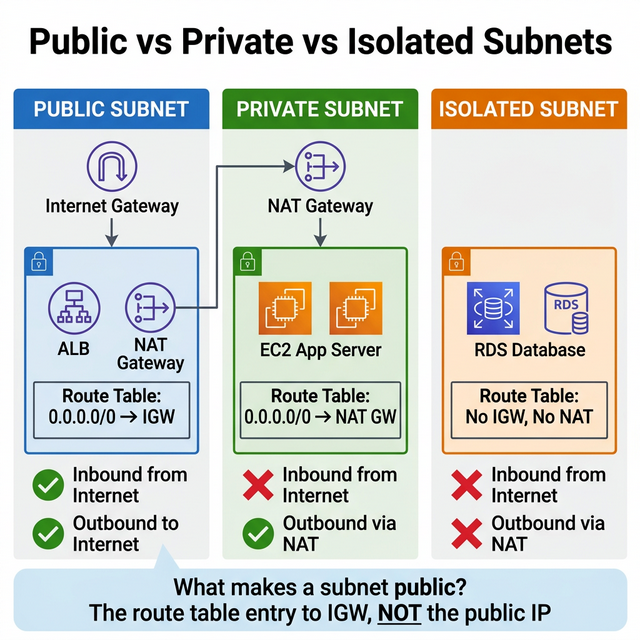
| Tier | Subnet Type | Contains | Internet Access |
|---|---|---|---|
| Public | Public subnet | ALB, NAT Gateway, Bastion (if any) | Direct via Internet Gateway |
| Private App | Private subnet | EC2, ECS, Lambda (VPC), EKS nodes | Outbound only via NAT Gateway |
| Private Data | Private subnet | RDS, ElastiCache, OpenSearch | No internet access (most secure) |
| Transit | Private subnet | Transit Gateway attachments, VPN | Routes to on-premises |
Multi-Account VPC Strategy (Enterprise)
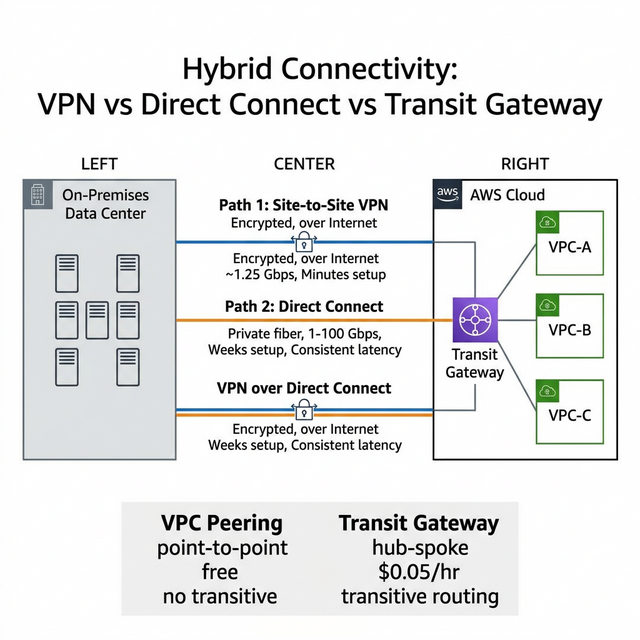
- Hub-and-Spoke — Central "shared services" VPC (DNS, logging, security) connected to workload VPCs via Transit Gateway. Each team gets isolated VPCs.
- Non-overlapping CIDRs — Plan CIDR blocks upfront using IPAM (VPC IP Address Manager). Overlapping CIDRs = impossible to peer or route.
- AWS Organizations + RAM — Share subnets across accounts using Resource Access Manager. One networking team manages VPCs, app teams deploy into shared subnets.
🎯 Key Takeaway
Interview tip: Say: "I design VPCs with a /16 CIDR, 3 tiers of subnets across 3 AZs (public, private-app, private-data), non-overlapping ranges planned with IPAM. For multi-account, I use Transit Gateway as a hub with spoke VPCs per workload, shared via RAM. This gives network isolation with centralized control."