AWS Services for Interviews
Key AWS services to know for solutions architect and cloud engineer interviews, organized by domain with one-liner descriptions:
Compute
- EC2 — Virtual servers with full OS control; choose instance type for CPU/memory ratio
- Auto Scaling — Automatically adjusts EC2 count based on demand (target tracking, step, scheduled)
- Lambda — Run code without servers; 15-min max, 10GB memory, pay per invocation
- EKS — Managed Kubernetes control plane; you manage worker nodes or use Fargate
- ECS — AWS-native container orchestrator; simpler than K8s, tight AWS integration
- Fargate — Serverless compute for ECS/EKS; no EC2 to manage, pay per vCPU+memory
Storage
- S3 — Object storage; 11 9s durability, lifecycle policies, 6 storage classes
- EBS — Block storage attached to EC2; gp3 (general), io2 (high IOPS), st1/sc1 (throughput)
- EFS — Managed NFS; shared across AZs, auto-scales, good for containers
- FSx — Managed file systems (Lustre for HPC, NetApp ONTAP for enterprise, Windows)
Database
- RDS — Managed relational DB (MySQL, PostgreSQL, Oracle, SQL Server); Multi-AZ for HA
- Aurora — Cloud-native relational; 5x MySQL perf, 6-way replication, Global Database
- DynamoDB — Serverless NoSQL; single-digit ms latency, auto-scales, Global Tables
- ElastiCache — In-memory caching (Redis or Memcached); sub-millisecond reads
- Redshift — Petabyte-scale data warehouse; columnar storage, Spectrum for S3 queries
Networking
- VPC — Isolated network; subnets, route tables, NACLs, security groups, NAT Gateway
- ALB — Layer 7 load balancer; path/host routing, WebSocket, gRPC support
- NLB — Layer 4 load balancer; ultra-low latency, static IPs, TCP/UDP
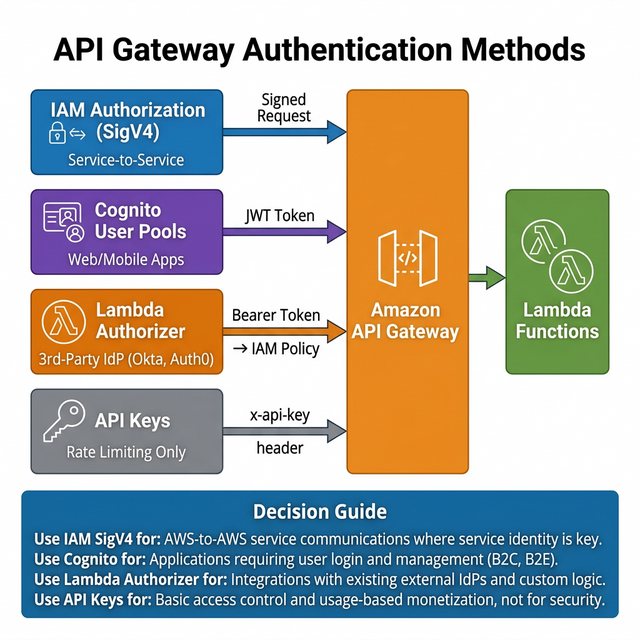
- API Gateway — Managed REST/WebSocket APIs; throttling, caching, auth integration
- CloudFront — Global CDN; 450+ edge locations, Lambda@Edge, Origin Shield
- Route 53 — DNS + health checks; routing policies (weighted, latency, failover, geolocation)
- Direct Connect — Dedicated private connection from on-prem to AWS; 1/10/100 Gbps
Security
- IAM — Users, roles, policies; always use least privilege, prefer roles over keys
- KMS — Managed encryption keys; integrates with S3, EBS, RDS, etc.
- WAF — Web Application Firewall; rate limiting, IP blocking, SQL injection/XSS protection
- Shield — DDoS protection; Standard (free) vs Advanced ($3k/mo, 24/7 DRT)
- GuardDuty — Threat detection using ML; analyzes CloudTrail, VPC Flow, DNS logs
- Secrets Manager — Rotate, manage, retrieve secrets; auto-rotation for RDS credentials
- AWS Config — Tracks resource configuration changes; compliance rules, remediation
- Security Hub — Centralized security findings from GuardDuty, Inspector, Macie, Config
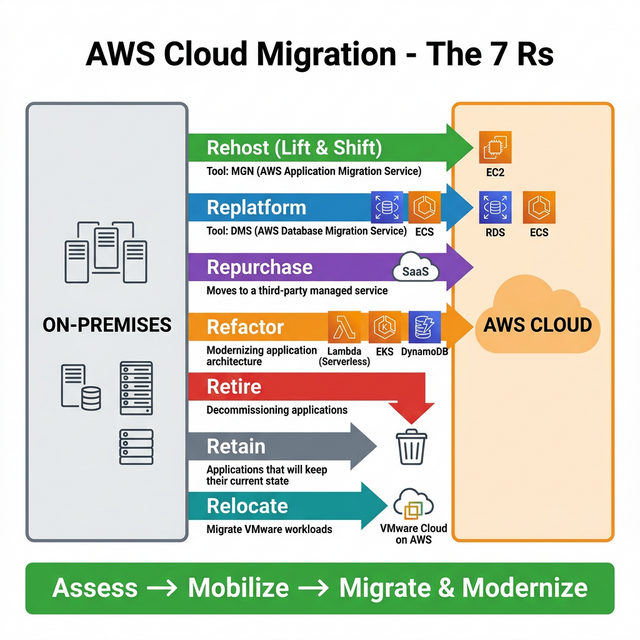
Migration
- DMS — Database Migration Service; supports homogeneous + heterogeneous migrations
- MGN — Application Migration Service; continuous replication for lift-and-shift
- Migration Hub — Central dashboard to track migration progress
- Snow Family — Physical devices for offline data transfer (Snowcone, Snowball Edge). Note: Snowmobile has been discontinued.
Event Driven
- SQS — Managed message queue; Standard (at-least-once) vs FIFO (exactly-once)
- SNS — Pub/sub messaging; fan-out to SQS, Lambda, HTTP, email, SMS
- EventBridge — Serverless event bus; content-based filtering, schema registry
- Step Functions — Visual workflow orchestrator; Standard (long) vs Express (high-volume)
Observability
- CloudWatch — Metrics, logs, alarms, dashboards; custom metrics, Log Insights queries
- CloudTrail — API call audit log; who did what, when, from which IP
- X-Ray — Distributed tracing; trace requests across microservices, find bottlenecks
Gen AI
- Bedrock — Managed foundation models (Claude, Llama, Titan); RAG, fine-tuning, agents
- SageMaker — Full ML platform; build, train, deploy custom models at scale
- Amazon Q — AI assistant for business (Q Business) and developers (Q Developer)
Cost Optimization
- Cost Explorer — Visualize and forecast AWS spending trends
- Compute Optimizer — Right-sizing recommendations for EC2, Lambda, EBS
- Savings Plans — Commit to $/hr for 1-3 yrs; up to 72% savings (flexible across services)
- Reserved Instances — Commit to specific instance type; up to 75% savings
- Spot Instances — Up to 90% savings; can be interrupted with 2-min warning
Analytics
- Athena — Serverless SQL queries on S3; pay per query, great for ad-hoc analysis
- Glue — Serverless ETL + Data Catalog; crawlers auto-discover schema
- EMR — Managed Spark/Hadoop; big data processing at petabyte scale
- Kinesis — Real-time data streaming; Data Streams, Firehose, Analytics
- QuickSight — Serverless BI dashboards; ML-powered insights, pay per session
Don't just list services — explain when and why you'd choose one over another. Example: "I'd use DynamoDB for single-digit ms reads on key-value data, but Aurora for complex joins and transactions." Interviewers want architectural reasoning, not memorization.